March 11, 2026 — Abstractions Lab announces the release of C5-DEC CAD v1.2. This release marks the most expansive functional milestone in the project’s history, delivering four new production-ready modules alongside significant enhancements to the SpecEngine, DocEngine, and Common Criteria tooling already present in the platform. For a visual stakeholder-oriented tour of C5-DEC CAD, visit the product presentation page. The release is now available on GitHub.
C5-DEC CAD is the open-source, AI-enabled toolkit for computer-aided secure system design, development, and evaluation that underpins the CyFORT project, carried out in the context of IPCEI-CIS. Where v1.0 established the stable core — Common Criteria Toolbox, SSDLC scaffolding, CPSSA, Transformer, and containerized dev environments — and v1.1 refined workspace management and AI-assisted design workflows, v1.2 substantially broadens the platform’s surface area. The release brings native CRA compliance automation, full SBOM lifecycle management, a self-contained cryptography module, an expanded CPSSA subsystem with threat modelling and quantitative risk analysis, and a richer SpecEngine and DocEngine layer. Together, these additions position C5-DEC CAD as an end-to-end secure engineering workbench that spans regulatory compliance, software supply chain security, threat modelling, structured specification management, and technical publishing — all from a single, traceability-first toolchain.
Key Highlights Of V1.2
CRA Compliance Automation For EU Regulation 2024/2847
The most strategically significant addition in v1.2 is a fully integrated CRA compliance module (c5dec/core/cra.py), directly targeting EU Regulation 2024/2847 (Cyber Resilience Act). The module covers Tier 1 of the CRA obligations with a YAML-backed requirements database of 35+ Annex I essential requirements, a Doorstop-integrated checklist engine with pass/fail/na verdict tracking and spreadsheet export annotated with per-category compliance percentages, a CRA Technical Documentation generator for all seven Annex VII chapters, and an EU Declaration of Conformity (DoC) generator for Annex V.
All three artefact types are accessible through the c5dec cra CLI command (create, verify, export), and the CRA Technical Documentation template is also reachable via the DocEngine pipeline (c5dec docengine cra-tech-doc). Feature flags and dedicated constants in c5settings.py ensure that CRA-specific configuration is kept clean and audit-ready.
Support for Default, Class I, Class II, and Critical CRA product risk classes is included, making the module applicable across the full range of products with digital elements subject to the regulation.
SBOM Lifecycle Management With Syft Integration
Complementing CRA compliance, v1.2 introduces a dedicated SBOM lifecycle management module exposed via the c5dec sbom CLI command (generate, import, diff, validate). Generation relies on Syft and supports both CycloneDX and SPDX output formats. Beyond generation, the module provides structured SBOM parsing and validation, version-to-version diff analysis for change visibility, and Doorstop traceability linking SBOM entries to specification items.
A key integration point is auto_verify_sbom_requirement(), which automatically cross-verifies the CRA essential requirement cra_ii_1_1 against the generated SBOM, tightening the loop between supply chain documentation and regulatory compliance.
This addition reflects the project’s broader philosophy that security artefacts should not exist in isolation: SBOM data, CRA verdicts, and Doorstop specification items are mutually linked, providing continuous, machine-verifiable traceability from product components to regulatory obligations.
A Native Python Cryptography Module
V1.2 introduces a self-contained cryptography module implementing a range of classical and modern operations directly in Python — without requiring external toolchain dependencies for the core operations. The module covers SHA-256 file integrity checking, GnuPG-based file signing and encryption, Shamir’s Secret Sharing over GF(2^127−1), and NaCl Ed25519 digital signatures.
All functionality is accessible through the c5dec crypto CLI command, which provides 11 subcommands: hash, verify-hash, sign, verify-sig, encrypt, decrypt, shamir-split, shamir-recover, nacl-keygen, nacl-sign, and nacl-verify. Prior to v1.2, the c5dec crypto command existed as a stub; it is now a fully dispatching implementation. Post-quantum cryptography capabilities remain accessible through the dedicated OQS-OpenSSL dev container, which continues to be supported alongside the new native module.
An Expanded CPSSA Subsystem With Threat Modelling & FAIR Risk Analysis
The Cyber-Physical System Security Assessment (CPSSA) module, introduced in v1.0, has been substantially expanded in v1.2. It is now structured as a proper multi-subsystem package, reflecting the increased breadth of its capabilities. The create_threat_model() function generates Threagile-compatible and OWASP pytm YAML threat models from Doorstop ARC artefacts through auto-discovery of architecture folders. A Threagile field-mapping subsystem (threagile-mappings.yml, threagile-schema.json) bridges the gap between C5-DEC’s specification model and Threagile’s input schema. Sidecar YAML files (threat-actors.yml, assumptions.yml) allow analysts to enrich threat models without modifying source Doorstop items.
Quantitative risk analysis has been added via generate_fair_input_template() and run_quantitative_risk_analysis(), with support for --fair-params YAML overrides and PERT distribution modelling for uncertainty-aware loss estimates. The c5dec cpssa CLI has been extended with fair-input and risk-analysis subcommands. A fully worked water-treatment system example provides a practical reference for applying the complete CPSSA workflow end-to-end.
SpecEngine And DocEngine Expansions
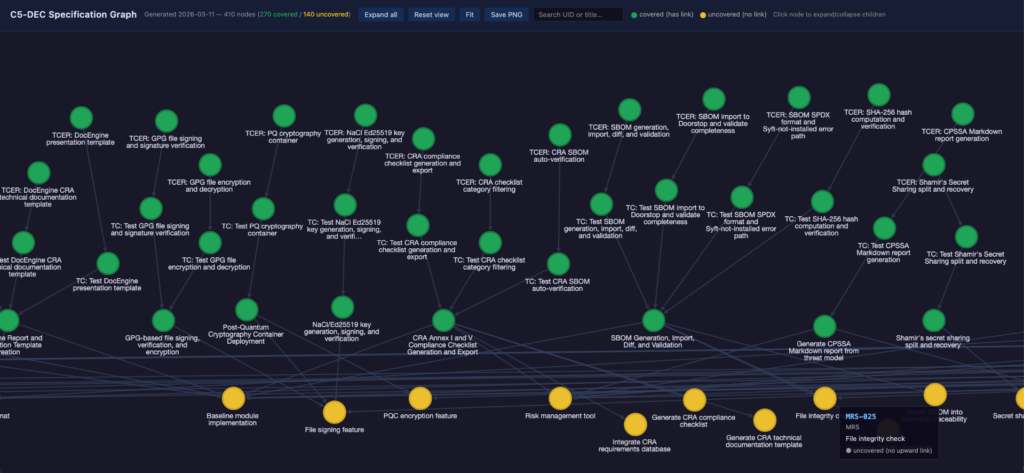
The SpecEngine toolkit gains four new tools in v1.2 and two significant upgrades to existing ones. c5graph.py produces an interactive, self-contained specs-graph.html traceability graph powered by Cytoscape.js with dagre layout, expand/collapse controls, and color-coded coverage indicators.
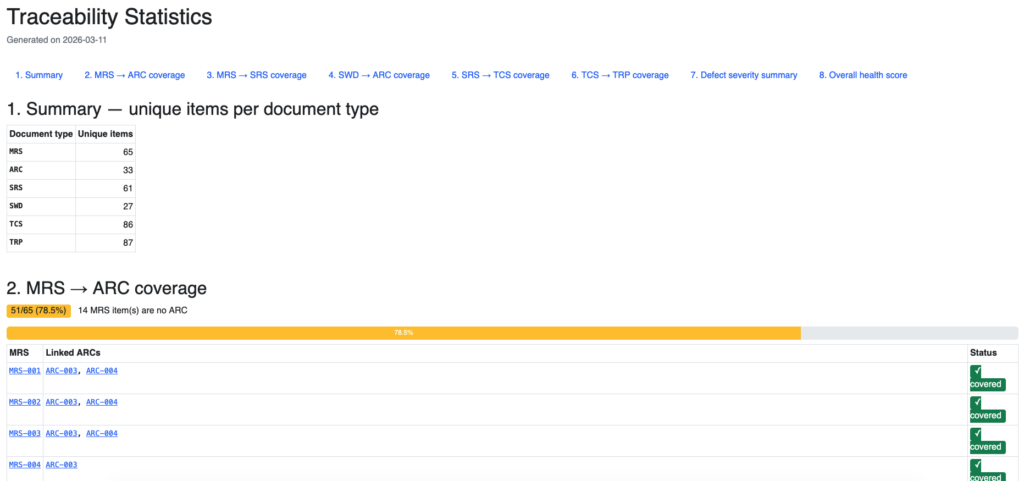
c5mermaid.py is a Mermaid-to-SVG/PNG pre-processor that renders fenced Mermaid blocks in Doorstop item files via mmdc, stores outputs in per-item assets/ directories, and replaces blocks with HTML comments preserving the original source; the transformation is idempotent and supports render, undo, and --dry-run modes. prune_bad_links.py removes malformed Doorstop links, and doorstop_yml_to_md.py migrates items from pure YAML to Markdown with YAML frontmatter; all four integrate with publish.sh. On the existing-tool side, c5browser.py — the standalone Bootstrap + DataTables HTML items browser — adds per-column filter inputs, dual .md/.yml format support, runtime document-type auto-discovery, and correct numeric column sorting.
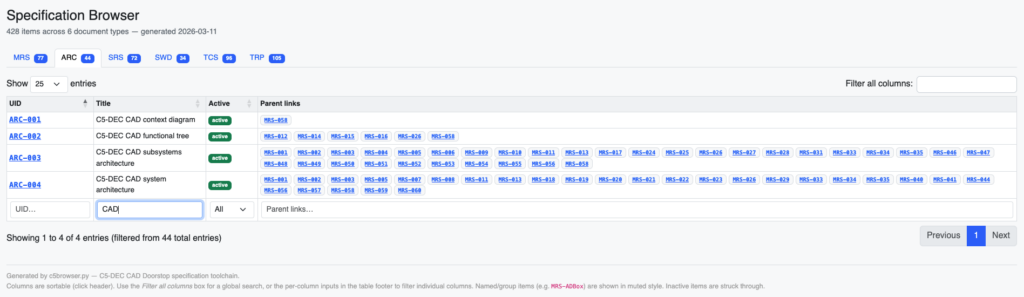
c5traceability.py has been generalized into a YAML-configurable, project-agnostic traceability analyzer with --config, --discover, and --discover-write flags and section-titled HTML navigation. Both continue to produce self-contained, offline-ready HTML output.
On the DocEngine side, v1.2 adds the c5dec docengine report|presentation -n <name> CLI command, which scaffolds ready-to-use document projects from report or presentation templates with variable substitution, overwrite protection, and Quarto dependency checking. The Quarto presentation template (c5dec/assets/presentation/) supports both Reveal.js and PowerPoint output with ALab branding and modular slide organization. A new c5dec_config_v2.yml configuration format with a matching custom_vars_v2.py pre-render script brings automatic LaTeX conversion, support for string/list/dict changelog entry formats, and LaTeX escaping for special characters. A dedicated docEngine.Dockerfile separates DocEngine dependencies (Quarto, TeX Live, Kryptor, Cryptomator CLI) from the lightweight C5-DEC dev container, which now lives in .devcontainer/c5dec-dev/.
Common Criteria Knowledge Base Completion And Quality Improvements
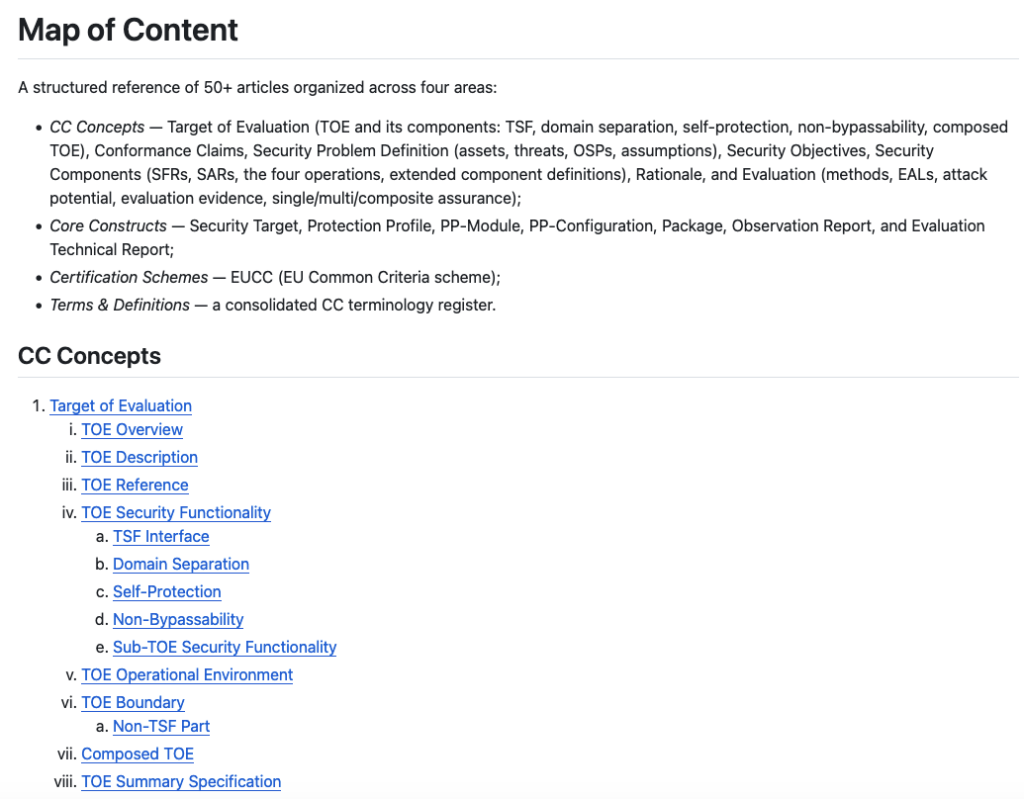
The CC concept wiki, introduced in earlier releases, has been completed with new articles and revisions to achieve full coverage of CC:2022. The knowledge base now spans 50+ structured articles across CC Concepts, Core Constructs, Certification Schemes (EUCC), and a Terms & Definitions register, making it directly usable as an LLM context source for AI-assisted CC evaluation workflows.
Unit test coverage has been significantly extended: new test files for CLI, ISMS, SSDLC, Transformer, CPSSA, and cryptography, bring total coverage to a level commensurate with a maturing engineering platform. Docker security hardening — non-root users, dropped Linux capabilities, --no-install-recommends, and package pinning — has been applied uniformly across Dockerfile, dev.Dockerfile, and docEngine.Dockerfile, and a .dockerignore file limits the build context. All Doorstop item files across arc, mrs, srs, swd, tcs, and trp documents have been migrated from pure YAML to Markdown with YAML frontmatter, and all document configs updated to itemformat: markdown.
Availability
C5-DEC CAD v1.2 product presentation page:
https://abstractionslab.github.io/c5dec/website/product-presentation.html
C5-DEC CAD v1.2 is available now as a free and open-source release on GitHub, including updated documentation, user manuals, a complete technical specification tree with traceability coverage:
https://github.com/AbstractionsLab/c5dec
A live specification browser at: https://abstractionslab.github.io/c5dec/traceability/index.html
Community feedback and contributions are welcome.