We are happy to announce the Beta release of SATRAP-DL!

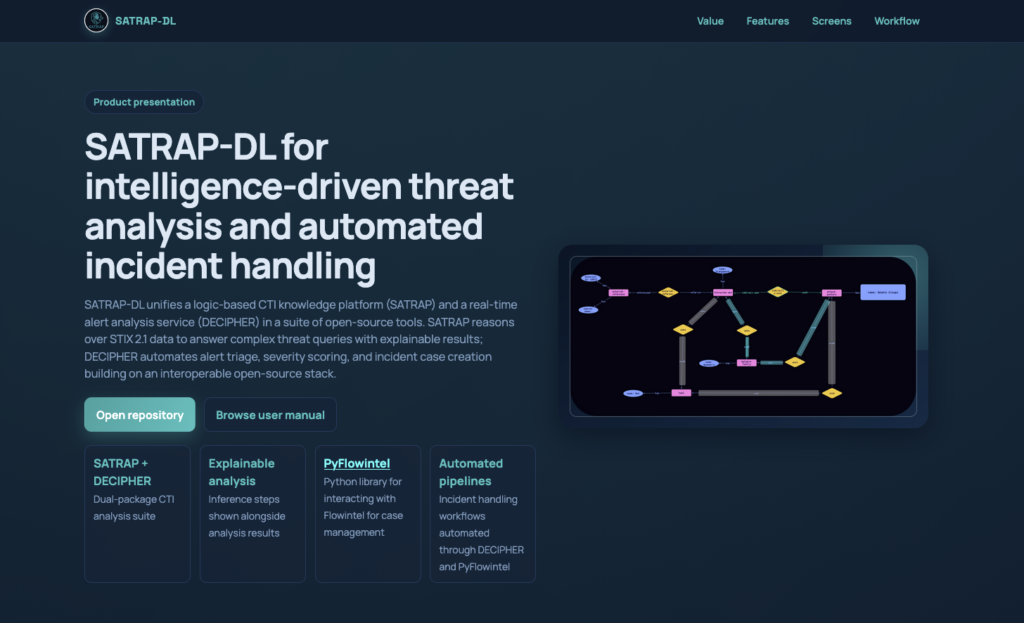
This update enriches the SATRAP-DL suite for intelligence-driven security operations with DECIPHER for automated incident handling, and PyFlowintel, a Python library for the Flowintel API.
What is DECIPHER?
DECIPHER (Detection, Enrichment, Correlation, Incident, Playbooks, Handling, Escalation and Recovery) is an open-source REST microservice for automated analysis and severity-confidence scoring of security alerts, informed by cyber-threat intelligence.
Where SATRAP reasons over stored CTI to answer complex threat queries with explainable inference, DECIPHER acts at the operational boundary: it receives live security alerts, searches for related threat intelligence, computes a severity score, and hands off prioritized incident cases to analysts, without manual intervention.
Together, SATRAP and DECIPHER form a unified suite for intelligence-driven threat analysis and automated incident handling when integrated with open-source tools such as the Wazuh-RADAR subsystem of IDPS-ESCAPE, the community-driven MISP threat intelligence platform and the Flowintel case management platform.
key features
- Simple deployment: Deploy a full stack working environment — DECIPHER, MISP, and Flowintel — with a single command.
- Automatic threat intelligence lookup: Get an analysis informed by real-time IOC search in MISP
- Transparent severity scoring: Obtain a severity-confidence score based on factors such as the threat level rate of the matched intelligence and sighting frequency and reliability of the CTI. The score and its breakdown are always visible to analysts.
- Incident case creation: Create prioritized cases in Flowintel so that analysts can start working on those that require more immediate attention.
- Live configuration updates: Tune scoring weights and runtime options at any time without restarting the service, to adjust as threat landscapes evolve.
- Ready for new threat scenarios: Add new threat scenarios as independent modules without touching the core code.
DECIPHER relies on PyFlowintel for managing cases in Flowintel. PyFlowintel is a Python library that wraps the Flowintel REST API in a clean, developer-friendly interface.
a typical DECIPHER workflow
You can build a DECIPHER automated pipeline spanning detection, enrichment, scoring, and escalation, relying completely on an open-source stack of tools: the Active Response module of RADAR, a subsystem of IDPS-ESCAPE, the DECIPHER REST analysis service, MISP and Flowintel.
A typical workflow run proceeds as follows:
1. Detect: RADAR detects a security alert matching a supported threat scenario and triggers DECIPHER.
3. Correlate and score: The scoring engine computes a severity-confidence score on the alert-related CTI factors.
5. Escalate: RADAR escalates flagged alerts to DECIPHER for creating prioritized cases in Flowintel with the incident context.
2. Enrich: DECIPHER searches for alert IOCs in MISP, extracting related CTI events, threat levels, sightings, and threat-identification tags.
4. Assign risk score and triage: RADAR computes the risk of the alert based on detection and the CTI score, and rates it.
6. Investigate and Recover: An analyst reviews the Flowintel case and decides recovery actions.
Get started
We invite you to try out the software and explore the full documentation and features.
end-users and security analysts
developers and contributors
Feel free to contact us with feedback, questions or feature requests at info@abstractionslab.lu.
