March 15, 2026 — Abstractions Lab announces the joint release of IDPS-ESCAPE v0.7 and v0.8. Together, these two releases represent the most significant functional leap in the project since RADAR was introduced in v0.4.
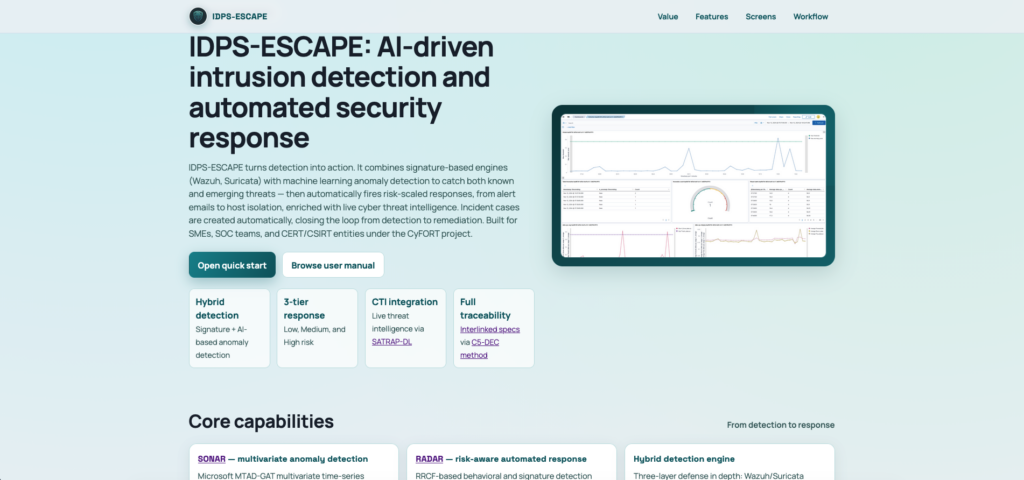
For a visual user-oriented tour of IDPS-ESCAPE, visit the product presentation page. The release is now available on GitHub.
v0.7 delivers SONAR — a production-grade multivariate anomaly detection engine — a risk computation model for RADAR, and the first structural integration of SATRAP-DL‘s DECIPHER subsystem. v0.8 completes that integration with a fully operational DecipherClient, adds health check and attack simulation tooling, and upgrades the SpecEngine and traceability layer to C5-DEC v1.2. Together, they close the loop on IDPS-ESCAPE’s MAPE-K (Monitor, Analyze, Plan, Execute, Knowledge) architecture: detection signals flow into a mathematically grounded risk engine, trigger risk-scaled automated responses enriched by live CTI, and generate Flowintel incident cases automatically — all within a fully traceable, specification-driven environment.
Key Highlights Of V0.7 And V0.8
SONAR: A Production-Grade Multivariate Anomaly Detection Engine
SONAR (SIEM-Oriented Neural Anomaly Recognition), the headline feature of v0.7, is a complete redesign of ADBox as a production-ready anomaly detection subsystem for Wazuh. Powered by Microsoft’s MTAD-GAT deep learning library, it operates directly on Wazuh alert streams through a YAML-based scenario system that makes detection workflows fully repeatable and version-controllable without touching Python code. Four pre-built scenario templates ship out of the box; a debug mode enables full offline train-detect cycles without a live Wazuh instance. With SONAR reaching production status, ADBox has been formally designated as a legacy research engine.
A Risk Engine And Three-Tier Automated Response For RADAR
v0.7 replaces RADAR’s ad-hoc per-scenario decision logic with a principled weighted fusion model: the normalized risk score
combines anomaly detection signal A, signature-based risk S, and DECIPHER CTI score T. The score drives a three-tier response system — notification, remediation with case creation, and full host isolation — implemented in a single consolidated active response script (radar_ar.py) that replaces the previous fragmented per-scenario implementations. v0.8 refines the tier boundaries and separates per-tier mitigation configuration for finer operational control.
DECIPHER Integration: From Stub To Full Production Client
v0.7 introduced a SatrapClientMock stub establishing the DECIPHER interface contract; v0.8 replaces it with a fully operational DecipherClient communicating with DECIPHER’s REST API. When RADAR fires a medium- or high-risk response, DecipherClient queries DECIPHER for MISP-backed IOC assessments, receives a CTI score, fuses it into the overall risk score, and opens a structured Flowintel case — all without manual SOC intervention.
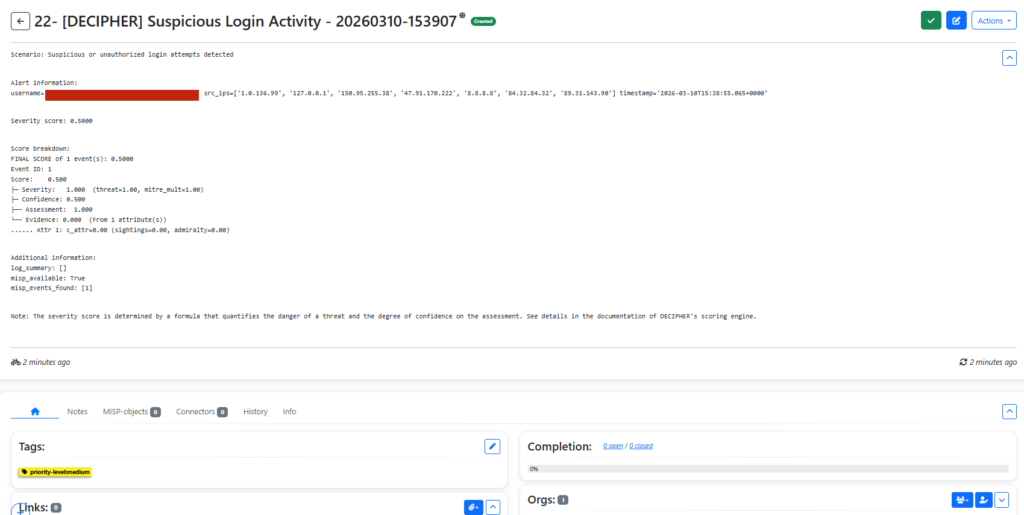
Flowintel incident cases created automatically by DECIPHER with full RADAR context: scenario, detection type, risk tier, CTI breakdown, and IOC set.
RADAR Health Checks And Attack Simulation
v0.8 adds a health check tool, an Ansible-driven diagnostic framework that verifies the reachability and functional status of all RADAR stack components on both manager and agent nodes. Complementing it, an attack simulation tool provides a controlled harness for exercising all three production scenarios — GeoIP anomaly, log volume change, and suspicious login — using dedicated Python simulation modules, with a companion Ansible playbook extending simulation support to remote agents.
SpecEngine Tooling And Traceability Infrastructure
v0.8 consolidates all SpecEngine scripts from C5-DEC v1.2, adding c5graph.py (interactive Cytoscape.js specification graph), c5mermaid.py (Mermaid-to-SVG/PNG rendering for Doorstop items), and prune_bad_links.py (automated link hygiene). The existing c5traceability.py and c5browser.py have been upgraded with richer coverage metrics, per-column filtering, and correct numeric sorting, and both are now integrated into the publish.sh workflow.
Specification Completeness, TRP Consolidation, And Product Website
New and revised HARC, LARC, and SWD items achieve technical specification completeness across RADAR and SONAR, with explicit source-file references replacing verbose pseudocode. The previously separate TRA and TRB test execution document types have been merged into a unified TRP (Test Case Execution Report) format. v0.8 also introduces the IDPS-ESCAPE product presentation page, providing a user-oriented visual overview of the platform.
Availability
IDPS-ESCAPE v0.8 product presentation page:
https://abstractionslab.github.io/idps-escape/website/product-presentation.html
IDPS-ESCAPE v0.7 and v0.8 are available now as free and open-source releases on GitHub, including updated documentation, user manuals, Ansible deployment automation, and a complete technical specification tree with traceability coverage:
https://github.com/AbstractionsLab/idps-escape
A live specification browser and traceability statistics report at:
https://abstractionslab.github.io/idps-escape/traceability/index.html
Community feedback and contributions are welcome.